Threat Intelligence & Abuse Response 网络运营中心
威胁情报与滥用响应
Document Version 1.0 发布于 2026 年 5 月 6 日
文档版本 1.0
Threat Intelligence Advisory
威胁情报通报
Investigation Report:
UnionPay-Impersonation Phishing Infrastructure
调查报告:
仿冒中国银联钓鱼基础设施
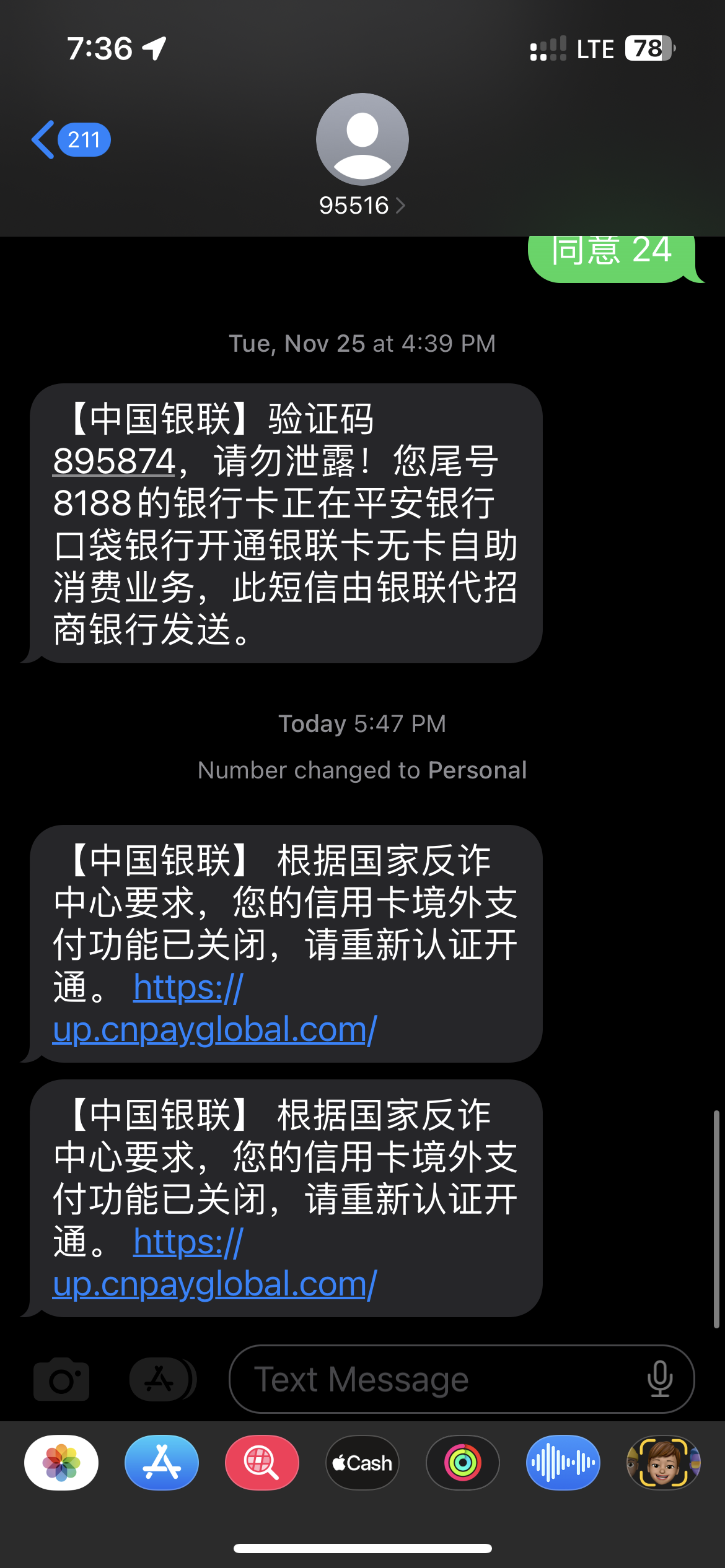
SMS-delivered lure impersonating China UnionPay, targeting cardholder credentials and one-time passwords in the Tokyo metropolitan area; correlated to a domain cluster hosted on 104.225.145.101 (AS25820 / IT7 Networks Inc).
仿冒中国银联的短信钓鱼活动,针对东京都地区的银联持卡人采集银行卡验证信息和短信一次性验证码;关联到托管于 104.225.145.101(AS25820 / IT7 Networks Inc)的域名集群。
1. Abstract摘要
This report documents a high-confidence payment-card phishing incident in which SMS messages impersonating China UnionPay directed the victim to https://up.cnpayglobal.com/. The incident occurred shortly after a payment activity near 〒104-0061 Tokyo, Chuo City, Ginza, 3 Chome-3-13, at approximately 35.6728586, 139.7624018. The fraudulent site collected payment-card verification data and SMS one-time passwords; subsequent banking notifications recorded an attempted online payment of CNY 11,987.95.
本报告记录一起高置信度的银行卡钓鱼事件。攻击者通过仿冒"中国银联"的短信,引导受害人访问 https://up.cnpayglobal.com/。事件发生于受害人在日本〒104-0061 东京都中央区银座 3 丁目 3-13 附近消费之后,坐标约为 35.6728586, 139.7624018。钓鱼网站收集银行卡验证信息和短信一次性验证码;其后受害人收到银行关于人民币 11,987.95 元网上支付的验证短信。
Technical investigation links the observed lure domain and related infrastructure to a cluster hosted on 104.225.145.101, associated with IT7 Networks Inc. and AS25820. The phishing site additionally presents implementation characteristics consistent with a Vite.js-built web application. RDAP records show consistent use of NameSilo, DNSOWL nameservers, and PrivacyGuardian privacy protection across the cluster.
技术分析显示,主要诱导域名及关联基础设施属于托管在 104.225.145.101 的域名集群,该 IP 与 IT7 Networks Inc 及 AS25820 相关。钓鱼网站还呈现出与 Vite.js 构建的 Web 应用一致的实现特征。RDAP 记录显示,该域名集群普遍使用 NameSilo 注册商、DNSOWL nameserver 和 PrivacyGuardian 隐私保护。
Keywords
phishing · UnionPay impersonation · SMS spoofing · payment-card fraud · RDAP · NameSilo · AS25820
关键词
钓鱼攻击 · 中国银联仿冒 · 短信发送方标识伪造 · 银行卡欺诈 · RDAP · NameSilo · AS25820
2. Incident Overview事件概述
Shortly after a payment activity near 〒104-0061 Tokyo, Chuo City, Ginza, 3 Chome-3-13, the victim received SMS messages impersonating China UnionPay. The message claimed that the victim's overseas payment capability had been disabled and instructed re-authentication through https://up.cnpayglobal.com/. The destination presented a UnionPay-themed card authentication interface and requested sensitive cardholder information, including card number, CVV/CVN2, expiration date, mobile telephone number, and SMS verification code.
受害人在日本〒104-0061 东京都中央区银座 3 丁目 3-13 附近消费后不久,收到仿冒"中国银联"的短信。短信声称受害人的信用卡境外支付功能已关闭,并要求通过 https://up.cnpayglobal.com/ 重新认证。该网站展示仿银联的银行卡认证界面,并要求填写银行卡号、CVV/CVN2、有效期、手机号和短信验证码等敏感信息。
Following selection of the verification-code function, the page remained in a loading state for approximately one to two minutes. This delay is consistent with a live-relay or operator-assisted fraud workflow. One plausible hypothesis is that the backend operators were manually entering the submitted card details into a downstream purchase flow, such as airline-ticket or hotel bookings sometimes associated with low-price proxy-purchase fraud. This is an inference from the observed behaviour and subsequent bank payment SMS, not direct proof of the downstream merchant or purchase category.
受害人点击获取验证码后,页面保持加载或转圈状态约 1 至 2 分钟。该延迟符合实时中继或人工辅助欺诈流程的特征。一种合理的调查假设是,后台人员可能正在将受害人提交的银行卡信息手动输入到下游消费流程中,例如机票或酒店订单;这类流程也可能与常见的低价机票、酒店代购欺诈相关。该判断基于页面行为和随后出现的银行支付验证短信,并不能直接证明具体下游商户或消费类别。
The phishing interface displayed an English option in the upper-right corner, but clicking it had no effect. The non-functional language switch, combined with the Chinese-language SMS lure and UnionPay-themed page content, supports the assessment that the campaign primarily targeted Chinese-speaking UnionPay cardholders physically present in Japan. The timing, location, and spoofed sender identity are also consistent with suspected SMS sender spoofing or pseudo-base-station activity; this remains an inference based on victim-side evidence pending carrier-side records.
钓鱼页面右上角显示 English 选项,但受害人观察到点击无效。结合中文短信诱导、银联主题页面和中文交互流程,该特征支持该活动主要面向身处日本的中文用户或中国银联持卡人的判断。短信发送方标识被仿冒,且事件与银座现场消费在时间和地点上高度相关,因此符合短信发送方标识伪造或伪基站活动的特征;该判断仍属于基于受害端证据的推断,若要最终确认短信投递机制,需要运营商侧日志或执法机关调取的电信记录。
The one-to-two-minute verification-code delay is consistent with live relay or operator-assisted fraud; the precise downstream purchase workflow remains an investigative hypothesis pending corroborating telemetry from the card issuer.
获取验证码后 1 至 2 分钟的加载延迟符合实时中继或人工辅助欺诈流程的特征;具体的下游消费流程仍属调查假设,须等待发卡行侧的关联遥测予以印证。
3. Documentary Evidence证据
The following screenshots constitute primary victim-side evidence, documenting the SMS lure, bank verification messages, phishing landing page, and credential collection form.
以下截图为主要受害端证据,分别记录诱导短信、银行支付验证短信、钓鱼落地页和银行卡信息收集表单。
https://up.cnpayglobal.com/.https://up.cnpayglobal.com/。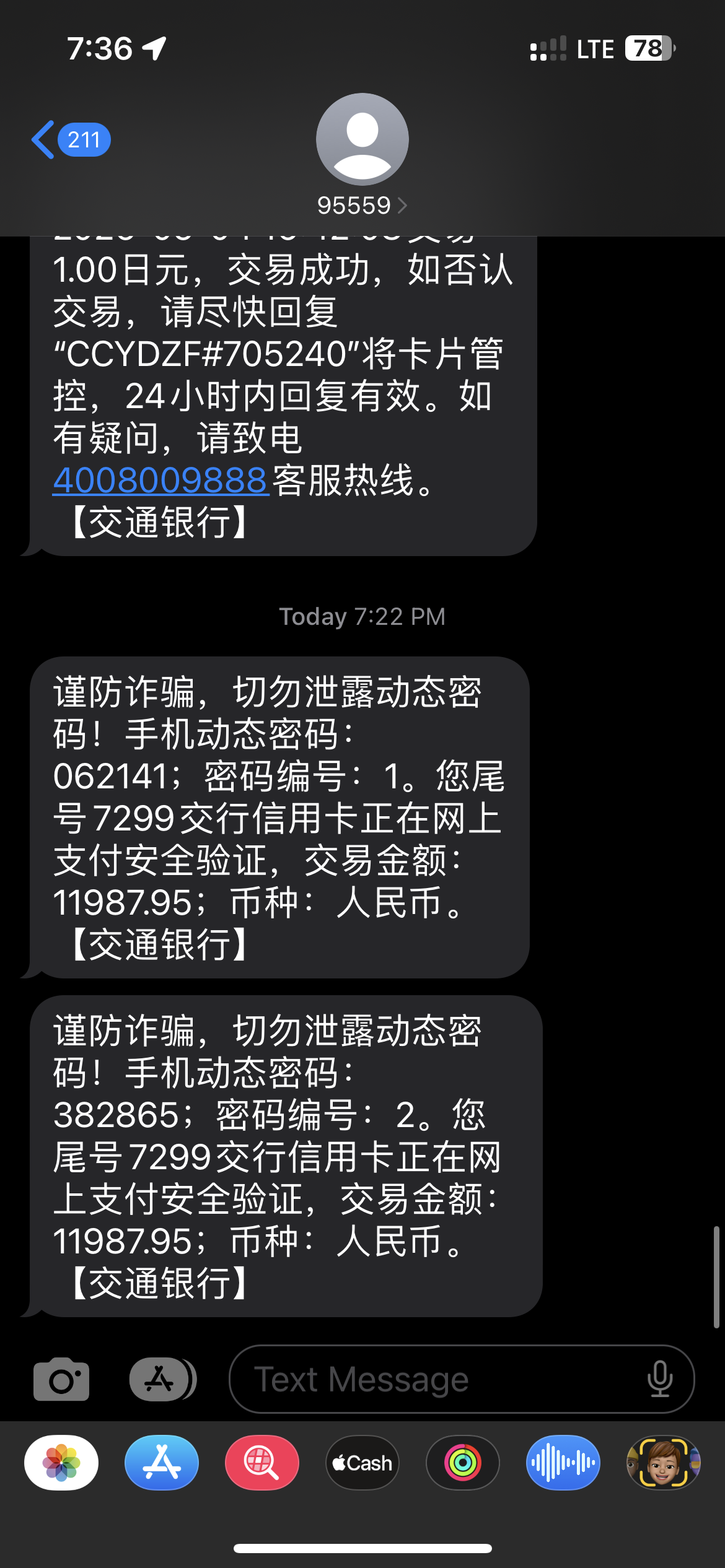
up.cnpayglobal.com 钓鱼落地页展示仿银联银行卡认证弹窗。4. Attack Chain Analysis攻击链分析
- The victim completed a payment activity near 〒104-0061 Tokyo, Chuo City, Ginza, 3 Chome-3-13.
- The victim received SMS messages impersonating China UnionPay.
- The SMS messages directed the victim to
https://up.cnpayglobal.com/. - The phishing page requested full card verification data and SMS OTP.
- The verification-code request remained in a loading state for approximately one to two minutes, suggesting possible live relay or operator-assisted backend interaction with a real payment workflow.
- A plausible investigative hypothesis is that the submitted card details were being manually used for downstream purchases, such as airline-ticket or hotel bookings; this has not been independently confirmed.
- The upper-right English option on the phishing page was non-functional, suggesting the workflow was designed primarily for Chinese-speaking users in Japan.
- The victim received bank verification messages for an attempted CNY 11,987.95 online payment.
- The victim identified the website as phishing and reported it to the registrar, registry, and hosting network.
- 受害人在日本〒104-0061 东京都中央区银座 3 丁目 3-13 附近完成消费。
- 受害人收到仿冒中国银联的短信。
- 短信诱导受害人访问
https://up.cnpayglobal.com/。 - 钓鱼页面要求输入完整银行卡验证数据和短信一次性验证码。
- 获取验证码后页面加载约 1 至 2 分钟,疑似攻击者在后台实时中继或人工对接真实支付流程。
- 一种合理的调查假设是,提交的银行卡信息被人工用于下游消费,例如机票或酒店订单;该点尚未被独立证实。
- 钓鱼页面右上角 English 按钮点击无效,说明该流程更可能主要面向在日本的中文用户。
- 受害人随后收到银行短信,提示一笔人民币 11,987.95 元的网上支付验证。
- 受害人确认该网站为钓鱼网站,并已向注册商、注册局和托管网络举报。
5. Infrastructure Indicators基础设施指标
5.1 Primary indicators of compromise5.1 主要失陷指标
| Indicator指标 | Value值 |
|---|---|
| Primary lure host主要诱导主机 | up.cnpayglobal.com |
| Root domain根域名 | cnpayglobal.com |
| Hosting IP托管 IP | 104.225.145.101 |
| Web build frameworkWeb 构建框架 | Vite.js (observed bundler signature)Vite.js(观察到的打包器特征) |
| ASN | AS25820 · IT7NET |
| Registrar注册商 | NameSilo, LLC · IANA ID 1479 |
| Registrar abuse注册商 abuse | [email protected] |
| IP / ASN abuseIP / ASN abuse | [email protected] |
| NameserversNameserver | NS1.DNSOWL.COM, NS2.DNSOWL.COM, NS3.DNSOWL.COM |
5.2 Related infrastructure on 104.225.145.1015.2 104.225.145.101 上的关联基础设施
FOFA-derived asset data identifies a cluster of similarly themed "Bank Card Authentication" hosts colocated on the same IP address.
FOFA 资产数据显示,同一 IP 上聚集多个以"银行卡认证"为主题的相似站点,构成同一基础设施集群。
| Host主机 | Port(s)端口 | Page title页面标题 | Root domain根域名 |
|---|---|---|---|
cn.lianhezf.com | 80 / 443 | Bank Card Authentication银行卡认证 | lianhezf.com |
cn.up-hwrz.com | 80 / 443 | Bank Card Authentication银行卡认证 | up-hwrz.com |
cn.yinlianasia.com | 80 / 443 | Bank Card Authentication银行卡认证 | yinlianasia.com |
cn.uphwzf.com | 80 / 443 | Bank Card Authentication银行卡认证 | uphwzf.com |
cn.yinlianworld.com | 80 / 443 | Bank Card Authentication银行卡认证 | yinlianworld.com |
cn.jingwaizf.com | 80 / 443 | Bank Card Authentication银行卡认证 | jingwaizf.com |
zgyinlian-zf.com | 80 / 443 | Bank Card Authentication / 400银行卡认证 / 400 | zgyinlian-zf.com |
cn.uprenzheng.com | 80 / 443 | Bank Card Authentication银行卡认证 | uprenzheng.com |
cn.upjprz.com | 80 / 443 | Bank Card Authentication银行卡认证 | upjprz.com |
zhifu-oversea.comcn.zhifu-oversea.com | 80 / 443 | Bank Card Authentication / blank银行卡认证 / 空 | zhifu-oversea.com |
104.225.145.101 | 80 / 443 / 888 / 22 | Bank Card Authentication / 400 / 403银行卡认证 / 400 / 403 | — |
6. RDAP and WHOIS FindingsRDAP 和 WHOIS 结果
Registry dates below are based on Verisign RDAP unless otherwise noted. Registrar-side dates may differ by one calendar day, as NameSilo reports normalized registrar dates separately from the Verisign timestamp.
下表中的注册时间主要采用 Verisign 注册局 RDAP。NameSilo 注册商侧日期有时会显示为前一日,这是注册商侧归一化日期与注册局精确 UTC 时间戳之间的差异。
6.1 Domain RDAP summary6.1 域名 RDAP 摘要
| Domain域名 | Status at query time查询时状态 | Registration (UTC)注册时间 (UTC) | Expiration (UTC)到期时间 (UTC) |
|---|---|---|---|
cnpayglobal.com | client transfer prohibited | 2026-05-05 01:35:56 | 2027-05-05 01:35:56 |
lianhezf.com | client transfer prohibited | 2026-04-02 03:45:27 | 2027-04-02 03:45:27 |
up-hwrz.com | client transfer prohibited | 2025-12-20 05:55:48 | 2026-12-20 05:55:48 |
yinlianasia.com | client hold; client transfer prohibited | 2026-04-21 03:27:59 | 2027-04-21 03:27:59 |
uphwzf.com | client transfer prohibited | 2025-12-25 08:15:20 | 2026-12-25 08:15:20 |
yinlianworld.com | client hold; client transfer prohibited | 2026-04-04 03:08:18 | 2027-04-04 03:08:18 |
jingwaizf.com | client hold; client transfer prohibited | 2025-11-19 08:25:35 | 2026-11-19 08:25:35 |
zgyinlian-zf.com | client transfer prohibited | 2025-11-22 17:22:02 | 2026-11-22 17:22:02 |
uprenzheng.com | client hold; client transfer prohibited | 2025-12-13 04:15:48 | 2026-12-13 04:15:48 |
upjprz.com | client hold; client transfer prohibited | 2025-12-13 04:24:00 | 2026-12-13 04:24:00 |
zhifu-oversea.com | client hold; client transfer prohibited | 2025-12-06 03:07:12 | 2026-12-06 03:07:12 |
6.2 Common registrar and DNS pattern6.2 注册商和 DNS 共性模式
| Registrar注册商 | NameSilo, LLC (IANA ID 1479) |
| Registrar support注册商 support | [email protected] |
| Registrar abuse注册商 abuse | [email protected] · +1.480.524.0066 |
| Privacy service隐私保护服务 | PrivacyGuardian.org |
| Common privacy phone隐私记录电话 | +1.3478717726 |
| DNS providerDNS 服务商 | DNSOWL |
| DNSSEC | Not delegation-signed未进行 delegation signing |
6.3 Hosting RDAP — 104.225.145.1016.3 托管 RDAP — 104.225.145.101
| Network handle | NET-104-225-144-0-2 |
| Address range地址段 | 104.225.144.0 – 104.225.159.255 |
| Network name | CL-104-225-144-0-20 |
| Type / status类型 / 状态 | Assignment / active |
| IP registrantIP 注册主体 | IT7 Networks Inc · 530 W 6th Street, Los Angeles, CA 90014, USA |
| Related registrant关联注册主体 | Cluster Logic Inc |
| Abuse contactAbuse 联系方式 | [email protected] · +1-408-260-5757 |
| NOC / tech / adminNOC / 技术 / 管理 | [email protected], [email protected], [email protected] |
6.4 Hosting RDAP — AS258206.4 托管 RDAP — AS25820
| AS number | AS25820 |
| AS name | IT7NET |
| Status状态 | Active |
| Registrant注册主体 | IT7 Networks Inc |
| Registrant address注册主体地址 | 4974 Kingsway Ave, Suite 668, Burnaby, BC V5H 4M9, Canada |
| Abuse contactAbuse 联系方式 | [email protected] · +1-408-260-5757 |
| NOC / tech / adminNOC / 技术 / 管理 | [email protected], [email protected], [email protected] |
7. Assessment分析结论
This incident is assessed as a high-confidence UnionPay-themed payment-card phishing campaign. The conclusion is supported by the following observations:
综合判断,该事件为高置信度仿中国银联银行卡钓鱼攻击。主要依据如下:
- The SMS impersonates China UnionPay and directs the victim to a non-official, newly registered domain.
cnpayglobal.comwas registered on 2026-05-05, matching the incident window.- The phishing page solicits CVV/CVN2, expiration date, telephone number, and SMS verification code.
- A real bank payment verification SMS for CNY 11,987.95 followed the interaction.
- The one-to-two-minute verification-code delay is consistent with a live-relay workflow and may indicate operator-assisted downstream purchase attempts.
- The non-functional English option and Chinese-language interaction path support a target profile of Chinese-speaking UnionPay users in Japan.
- The site appears to have been implemented as a Vite.js-built web application, providing a useful technical fingerprint for log searches, file-system triage, and related-site clustering.
- FOFA asset data identifies many similarly themed "Bank Card Authentication" hosts on the same IP address.
- RDAP records demonstrate strong infrastructure overlap across registrar, DNS provider, privacy service, and hosting IP.
- Several related domains already show
client hold, suggesting prior abuse handling or takedown activity against the same cluster.
- 短信仿冒中国银联,并诱导访问非官方的新注册域名。
cnpayglobal.com注册于 2026-05-05,与事件时间窗口一致。- 钓鱼页面要求输入 CVV/CVN2、有效期、手机号和短信验证码。
- 页面交互后出现人民币 11,987.95 元真实银行支付验证短信。
- 获取验证码后的 1 至 2 分钟加载延迟符合实时中继流程特征,也可能指向人工辅助的下游消费尝试。
- English 按钮无效且主要交互路径为中文,支持"面向在日本中文用户或银联持卡人"的目标画像。
- 钓鱼网站疑似使用 Vite.js 构建,该技术指纹可用于日志检索、文件系统取证和关联站点聚类。
- FOFA 资产数据显示,同一 IP 上存在多个"银行卡认证"主题相似站点。
- RDAP 记录显示注册商、DNS 服务商、隐私保护服务和托管 IP 存在高度重合。
- 多个关联域名查询时已处于
client hold状态,说明该集群可能已被部分 abuse 流程识别或处置。
8. Actions Already Taken已采取行动
The domain cnpayglobal.com has been reported to NameSilo with a request for suspension of all DNS resolution. The matter has further been submitted to Verisign in its capacity as the .com registry, and the AS25820 / IT7 Networks abuse contact identified through RDAP has been notified.
受害人已经向 NameSilo 举报 cnpayglobal.com,并要求停止全部 DNS 解析。该事件也已提交给 .com 注册局 Verisign。受害人还通过 RDAP 查询到的 AS25820 / IT7 Networks abuse 联系方式提交了举报。
9. Current Status当前状态
The following table records the response status of each notified party as of the most recent update. This section will be revised as further responses are received.
下表记录截至最新更新时各被通知方的响应状态。后续收到回复时将持续修订本节。
| Party主体 | Status状态 | Disposition处置情况 |
|---|---|---|
| NameSilo, LLC Registrar注册商 |
Acknowledged · Action taken已确认 · 已处置 | NameSilo Support has replied and confirmed that cnpayglobal.com has been placed on ClientHold status, effectively suspending DNS resolution for the lure domain.NameSilo Support 已回复,确认 cnpayglobal.com 已被置于 ClientHold 状态,等同于停止该诱导域名的 DNS 解析。 |
| Verisign, Inc. .com Registry.com 注册局 |
Awaiting response等待回复 | Abuse submission acknowledged on receipt; no substantive response received at the time of this update.Abuse 提交已收到自动确认;截至本次更新尚未收到实质性回复。 |
| IT7 Networks Inc. AS25820 hosting networkAS25820 托管网络 |
Awaiting response等待回复 | RDAP-listed abuse contact [email protected] notified; no response received at the time of this update. Phishing content on 104.225.145.101 remains observable.已通过 RDAP 中列出的 [email protected] 提交举报;截至本次更新尚无回复。104.225.145.101 上的钓鱼内容仍可观测到。 |
NameSilo's ClientHold action removes the lure domain from DNS resolution but does not affect the underlying hosting infrastructure or related domains within the cluster. Sustained takedown still requires action from the hosting network and from the registry against the broader domain set.
NameSilo 设置的 ClientHold 仅停止该诱导域名的 DNS 解析,不影响底层托管基础设施或集群内的关联域名。要实现持续下架,仍需托管网络处理钓鱼内容,并由注册局对更大范围的域名集合采取行动。
10. Recommended Actions建议后续行动
Registrar & registry. NameSilo and Verisign should be requested to apply client hold or an equivalent suspension to cnpayglobal.com, review and suspend related domains, preserve registration / account / DNS logs, correlate PrivacyGuardian and NameSilo account metadata, and search for additional domains registered through the same account, payment method, login-IP history, or privacy profile.
注册商与注册局。建议要求 NameSilo 和 Verisign 对 cnpayglobal.com 设置 client hold 或等效暂停状态,复核并暂停关联域名,保全注册资料、账户登录记录和 DNS 变更日志,关联分析 PrivacyGuardian 和 NameSilo 账户元数据,并检索同账户、同付款方式、同登录 IP 或同隐私资料注册的更多域名。
Hosting network. IT7 Networks, Cluster Logic, and AS25820 should be requested to disable the phishing content on 104.225.145.101; preserve web-server, reverse-proxy, SSH, control-panel, operator-panel, browser-automation, and downstream order-submission logs alongside customer and payment records; identify and suspend the customer controlling the host; and search adjacent network space for similar UnionPay or overseas-payment phishing content. Because the site appears to use Vite.js, responders should also search for Vite build artifacts, hashed JS/CSS assets, source-map remnants, and deployment paths that may link this site to others.
托管网络。建议要求 IT7 Networks、Cluster Logic 和 AS25820 停止 104.225.145.101 上的钓鱼内容,保全 Web server 日志、反向代理日志、SSH 日志、控制面板日志、后台操作面板日志、浏览器自动化痕迹、下游订单提交日志、客户记录和付款记录,识别并暂停控制该主机的客户,并排查相邻网段中相似的银联或境外支付钓鱼页面。由于该站点疑似使用 Vite.js 构建,处置方还应检索 Vite 构建产物、带哈希的 JavaScript 和 CSS 资源、source map 残留以及部署路径,以关联其他同源站点。
Card issuer & carrier. The exposed card should be treated as compromised if card number, CVV/CVN2, expiration date, mobile number, or OTP were entered. The card issuer should replace the card; block online, overseas, and card-not-present transactions until replacement; and preserve risk and authorization logs for the attempted CNY 11,987.95 payment, including merchant descriptors, device fingerprints, transaction-channel metadata, and any airline, hotel, or travel-merchant indicators. The mobile carrier should be asked to investigate sender spoofing or pseudo-base-station activity near the Ginza location during the relevant time window.
发卡行与运营商。如果受害人输入过卡号、CVV/CVN2、有效期、手机号或验证码,应视为银行卡已泄露。建议发卡行立即换卡,在换卡前关闭线上、境外和非面对面支付能力,并保全人民币 11,987.95 元支付尝试的风控和授权日志,包括商户描述、设备指纹、交易渠道元数据,以及如存在则保全机票、酒店或旅行类商户线索。同时建议向手机运营商提交事件时间、地点和短信截图,要求调查银座附近是否存在短信发送方标识伪造或伪基站活动。
11. Conclusion结论
The collected SMS evidence, phishing-page screenshots, FOFA asset data, RDAP records, and Vite.js implementation fingerprint together support the conclusion that up.cnpayglobal.com and the related domains constitute coordinated payment-card phishing infrastructure impersonating China UnionPay. The one-to-two-minute verification-code delay and the non-functional English option further support a live-relay fraud workflow aimed at Chinese-speaking UnionPay cardholders in Japan. Immediate takedown, log preservation, and cross-provider correlation are warranted.
综合短信证据、钓鱼页面截图、FOFA 资产数据、RDAP 记录和 Vite.js 实现指纹,可以确认以 up.cnpayglobal.com 为核心的关联域名构成一组仿冒中国银联的银行卡钓鱼基础设施。获取验证码后的 1 至 2 分钟延迟,以及 English 按钮无效的中文交互流程,进一步支持"实时中继式欺诈"和"面向在日本中文银联用户"的判断。建议立即下线、保全日志,并由注册商、注册局、托管商、银行和运营商进行跨主体关联调查。
A. Appendix — Takedown List附录 — 处置列表
up.cnpayglobal.com cnpayglobal.com cn.lianhezf.com cn.up-hwrz.com cn.yinlianasia.com cn.uphwzf.com cn.yinlianworld.com cn.jingwaizf.com zgyinlian-zf.com cn.uprenzheng.com cn.upjprz.com zhifu-oversea.com cn.zhifu-oversea.com 104.225.145.101
OwO Network, LLC
OwO Network, LLC